A lot of folks online are being critical of Ubiquiti about releasing the UDM Pro with the features it has and the hardware it’s configured with, because they feel it does not have the same obvious market fit that most of their other hardware has always had prior to it.
I believe that the UDM Pro makes big economic sense for Ubiquiti, and will likely carry their “Gen2” products onwards to be their most successful lineup so far.
The UDM Pro is priced competitively ($379 USD) against their own Security Gateway Pro ($344 USD) while also being physically more powerful in every way. Nearly everyone is going to choose the newest one for $55 more over the older one (which is obsolete anyways) for the power capabilities alone.
Ubiquiti’s goal with the UDM Pro is to give everyone an appliance that can easily run Protect, Access, and Talk at the same time, to help them get a basic understanding of what they are and how they work (and inevitably outgrow them) at which point they can up-sell you to their dedicated Protect, Access, and Talk appliances. The UNVR for Protect is the only one of those available in the Early Access store, and I’m assuming dedicated Access and Talk controllers are in the pipeline.
If the UDM Pro were more expensive – say $500 USD, the value proposition against the USGP alone wouldn’t make much sense anymore, especially if you don’t need 10G and don’t care about having the newest hardware.
And if the UDM Pro were simply an upgraded Gateway without the hard drive bay and 8 port switch, it wouldn’t also replace their CloudKey appliances and wouldn’t be able to run Protect, Access, or Talk.
In my observations, the people being the most critical are the ones who should be the most excited: professional installers. They don’t seem to see (or care) how huge of an up-sell opportunity Ubiquiti has handed everyone with the UDM Pro being what it is. Now every networking client that asks “hey how about cameras/phones/nfc readers” already has what they need to get started and room to expand later.
On paper, the UDM Pro is not the most powerful device of its kind when compared to some Cisco or pfSense alternatives, but I think Ubiquiti is taking a page from the Apple playbook here, and trusting that their tight software integration will be enough of a draw to win people over, and I believe this will work out positively for them in the long run.
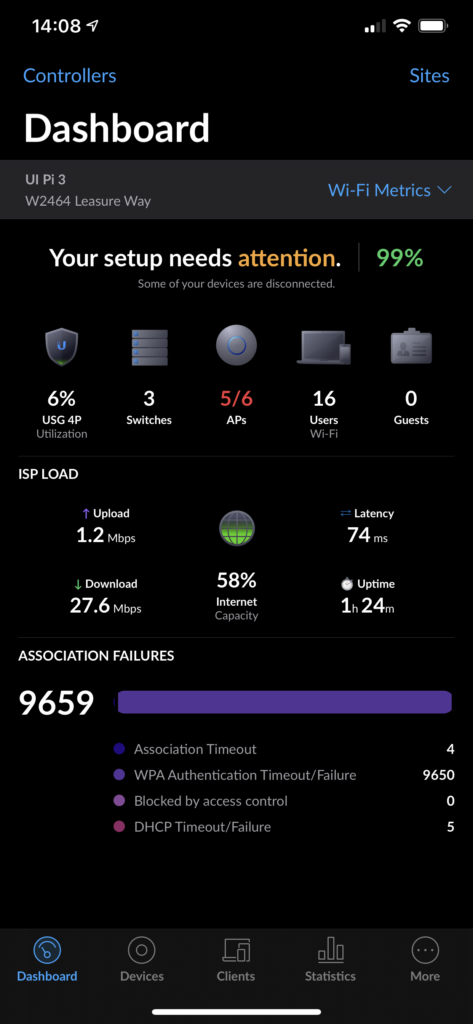
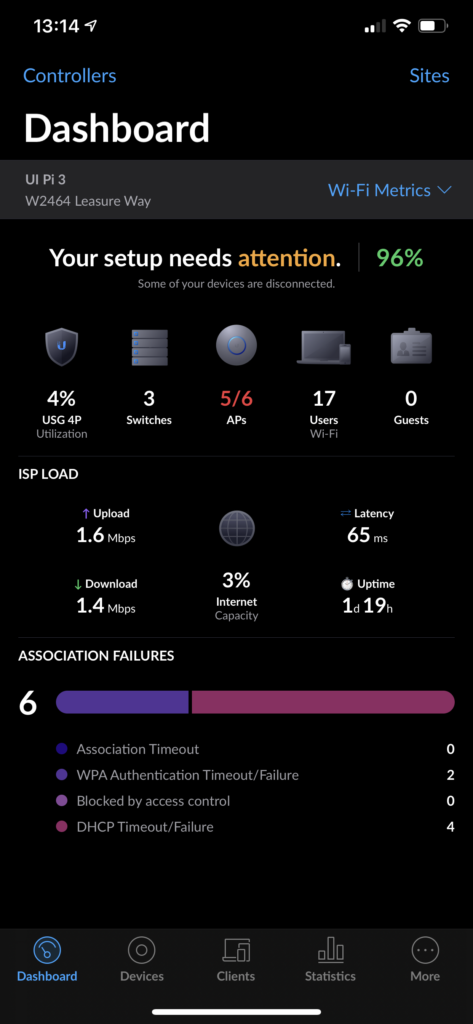
My UDM Pro will arrive this afternoon via UPS (shout out to our super cool UPS driver!) and I’m excited for it to replace the USGP and Raspberry Pi 3 in my server rack.